SOVEREIGN DIGITAL IDENTITY BLUEPRINT
Sovereignty • Systems Architecture • Anticipatory Governance
Diagnosing the structural limitations of NSW's physical identity architecture and designing the sovereign blueprint that became a global reference model for digital identity.
The Structural Condition
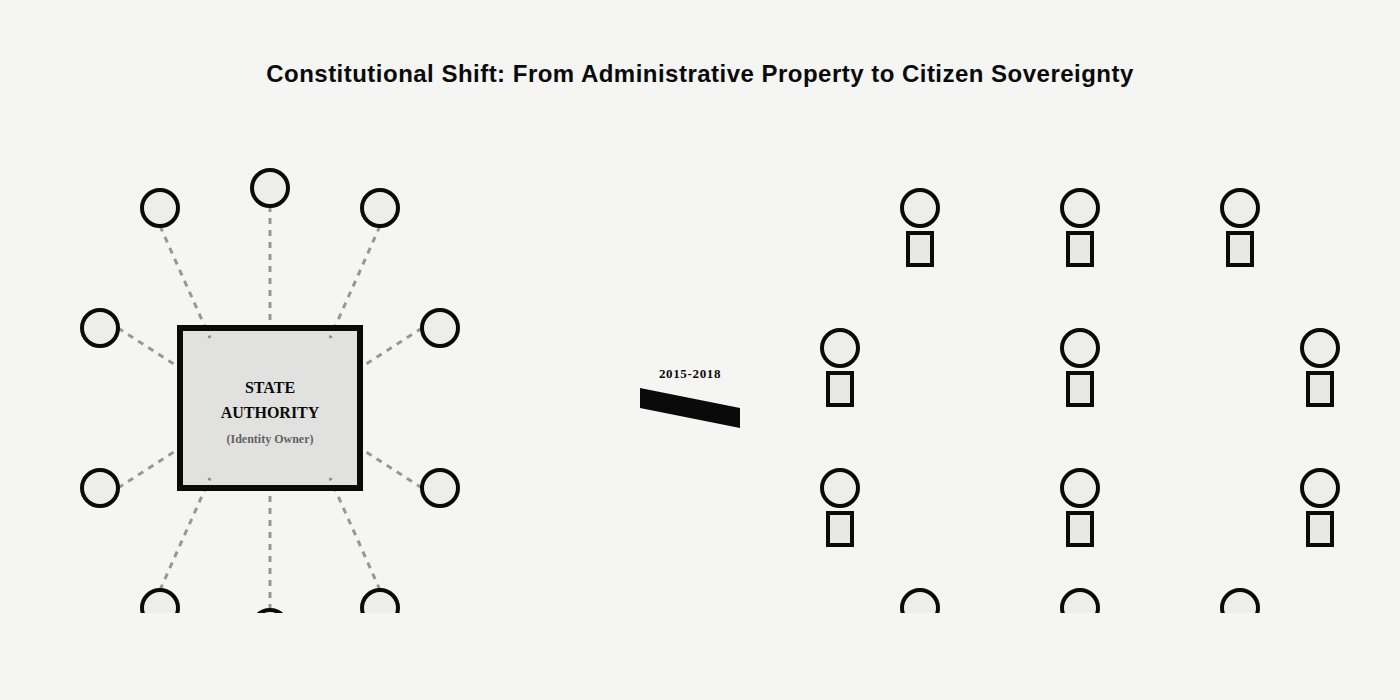
By 2015, the state-citizen identity relationship in NSW operated under a 20th-century paternalistic paradigm. Identity was administrative property. Citizens held permission slips. Proving identity required constant, friction-heavy recourse to the authority that already held the data.
Physical documents created compounding risk at every verification event. Proving age at a venue meant exposing home addresses and licence numbers. Every interaction carried data toxicity risk where the verification itself became a potential surveillance point.
The legislative architecture was equally rigid. The Road Transport Act 2013 defined a licence strictly as a physical card. A digital display had no legal standing for law enforcement or commercial verification, classified as a photograph of information with no statutory authority.
The 1991 DRIVES backend, built for batch processing and centralised control, was architecturally incapable of supporting real-time, citizen-initiated queries without risking cascading system failures or mass data harvesting. The infrastructure predated the conditions it was now being asked to serve by more than two decades.
THE ENGAGEMENT
Client: Department of Customer Service (NSW Government)
Role: Principal Institutional Designer, Sovereign Identity
Scope: Foundational design of the Architecture of Trust framework, spanning the institutional blueprint for sovereign transition, phased pilot sequencing from recreational credentials through to driver licences, and the legislative roadmap for cross-domain synchronisation across policing, transport, and privacy.
THE DIAGNOSTIC
The Legal-Technical Mismatch
Legislative metamorphosis was the primary structural challenge. Without synchronising transport law with policing powers, a citizen holding a valid digital licence remained exposed to phone seizure under conflicting statutes. The legal architecture had to be rebuilt before any technical implementation could proceed.
The Trust Hierarchy Problem
The architecture had to serve three principals simultaneously: Regulatory (police needing cryptographic certainty), Commercial (venues needing low-stakes confidence), and Sovereign (citizens needing data agency). Each principal carried different verification requirements. A single architecture had to satisfy all three without subordinating any.
The Sequencing Requirement
Launching directly with driver licences carried catastrophic failure risk. The diagnostic insight was to de-risk through sequencing, using low-consequence credentials (fishing and boat licences) as a beta-phase for the technical and legal stack. Each phase matured the architecture before the next credential category was loaded onto it.
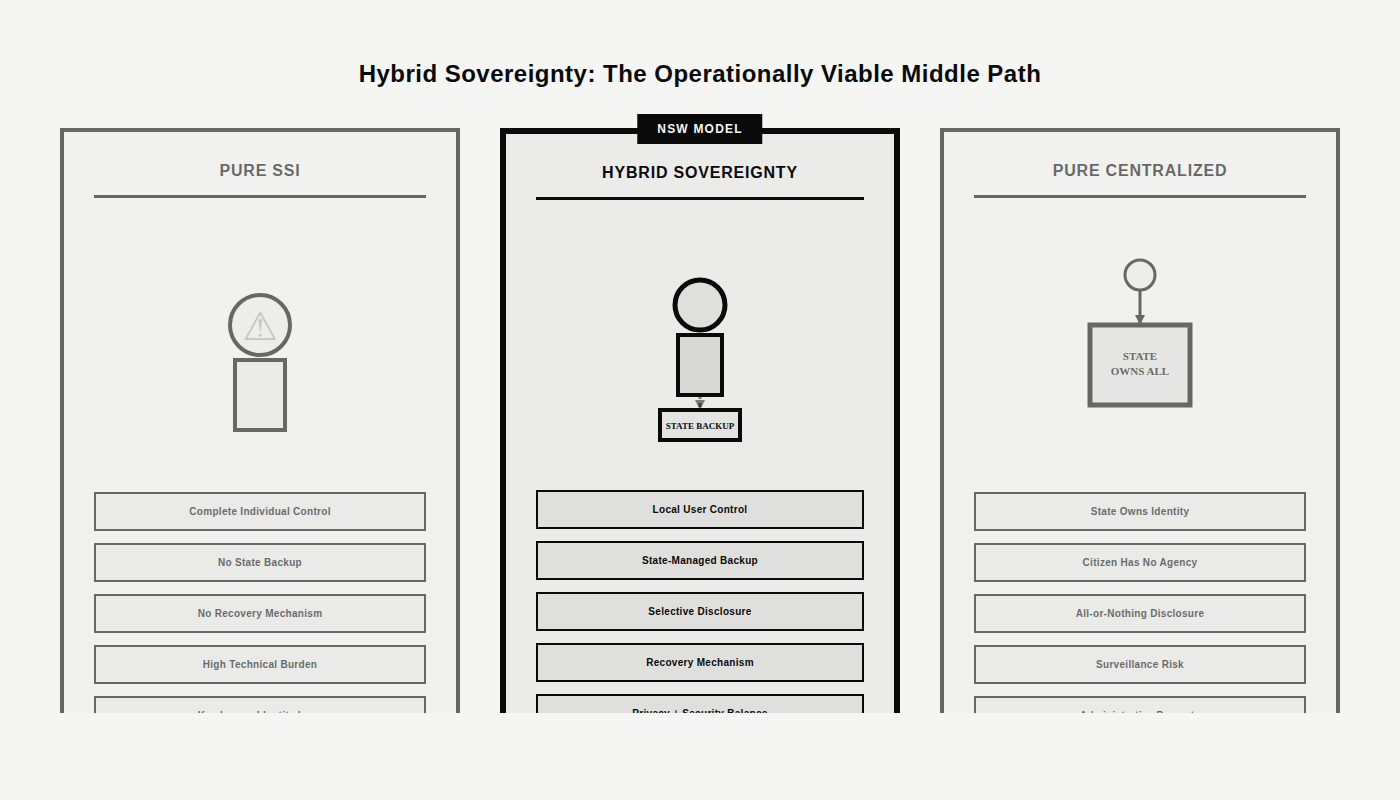
Hybrid Sovereignty
Pure self-sovereign identity (SSI) was operationally fragile for the general population. The solution was a sovereignty-mimetic model: local storage and selective disclosure providing the user experience of control, with state-managed backup authority preserved beneath the architecture. The citizen experiences sovereignty. The state retains the structural guarantee.
THE Architectural INTERVENTION
Phased Pilot Sequencing
A three-phase, risk-calibrated rollout. Recreational licences (Phase 1) and Photo Cards (Phase 2) matured the technical stack and built public trust at low consequence. Driver licences (Phase 3) deployed onto a proven architecture.
Privacy-by-Design: Attribute-Based Sharing
The verification logic was rebuilt around cryptographic assertion. A user proving they were over 18 transmitted a boolean confirmation that contained no birth date, address, or licence number. The identity interaction was de-risked at the protocol layer.
Multi-Actor Verification Ecosystem
A service blueprint providing police with real-time registry checks through Mobipol, venues with secure QR scans, and citizens with zero-knowledge style control over their personal data. Each actor received the verification layer appropriate to their function.
Legislative Equivalence
The legal scaffolding prohibited the seizure of devices during verification, ensuring the Architecture of Trust protected the citizen's broader digital privacy. This was the structural precondition for public adoption. Every technical capability depended on this legislative foundation being in place.
OUTCOMES
The phased architecture scaled to the full NSW Digital Driver Licence rollout (2019+), establishing a global template for ISO/IEC 18013-5 compliance cited by Estonia, South Korea, and the United States.
Visual display and cryptographic verification were separated into distinct trust layers. Police utilise real-time database checks through Mobipol for verification at the cryptographic layer. Spoofed visual displays carry no verification weight in the architecture.
The Once-Only principle became operational reality. Citizen-held credentials now maintain state-level security with individual agency embedded as a structural design principle.
The recreational-first pathway de-risked the full programme through iterative learning at each phase, establishing the sovereign proof of concept as a viable instrument of national resilience.
REQUIRED NEXT STEPS
The system must now evolve toward hardware-backed attestation and full backend modernisation through RegStar to eliminate the technical debt of the 1991 mainframe. AI-driven deepfakes represent the next category of threat the architecture must absorb.